The Health Insurance Portability and Accountability (HIPAA) Act sets the standard for handling protected health information (PHI) in the United States.
A healthcare app can look polished, ship on time, and still create serious risk. The problem usually is not the feature set. It is the lack of compliance planning behind the product. When HIPAA requirements are handled too late, teams run into issues with data access, storage, infrastructure, auditability, and third-party tools that should have been addressed much earlier.
For teams planning a secure digital health product, this changes the entire development approach. HIPAA compliant healthcare app development touches architecture, access control, data handling, vendor selection, and long-term operations.
This blog breaks down the compliance basics, essential features, technical architecture, common mistakes, evaluation criteria, and delivery considerations that matter before you start building.
What Makes a Healthcare App HIPAA Compliant?
A healthcare app does not become HIPAA compliant because it uses encryption or secure login alone. Compliance depends on how protected health information is handled across the full system.
That includes how PHI is collected, stored, accessed, shared, and monitored at every stage. If even one part of that flow is poorly controlled, the app can create privacy and security risk.
HIPAA compliant app development is about building reliable controls around sensitive data, not adding a single security layer at the end.
The Three Safeguard Layers That Shape Compliance
HIPAA compliance is usually shaped by three core safeguard areas.
-
Technical safeguards cover encryption, access control, authentication, audit logs, and secure data transfer.
-
Administrative safeguards focus on policies, internal procedures, risk assessments, team responsibilities, and vendor oversight.
-
Physical safeguards apply to how the infrastructure, devices, and hosting environment are secured against unauthorized access.
In simple terms, HIPAA compliant mobile app development depends on both the product and the operating model behind it. A secure app needs technical protection, responsible processes, and a controlled environment working together.
HIPAA Compliance Requirements at a Glance
When teams ask how to build a HIPAA compliant app, they usually focus first on features, but that’s not enough. Compliance depends on a set of technical, operational, and vendor-level controls working together.
This quick checklist gives a practical view of the core requirements that shape HIPAA compliant app development. It also helps readers scan the essentials before moving into the deeper sections on architecture, features, and implementation. If any of these controls are weak or missing, the app can create security, privacy, and compliance risks.
| Requirement |
What It Means |
| Encryption at rest and in transit |
Protect PHI when stored in databases, files, and while moving across networks |
| Authentication and MFA |
Verify user identity through secure login and multi-factor authentication where needed |
| Role-based access |
Limit data access based on user roles such as patient, provider, admin, or staff |
| Automatic session timeout |
Reduce unauthorized access risk by ending inactive sessions automatically |
| Audit logs |
Track who accessed, viewed, changed, or shared sensitive health data |
| Backup and recovery |
Maintain secure backups and recovery plans to protect data availability |
| BAA with vendors |
Sign Business Associate Agreements with vendors that handle PHI |
| Secure cloud infrastructure |
Use compliant hosting and infrastructure controls to support secure operations |
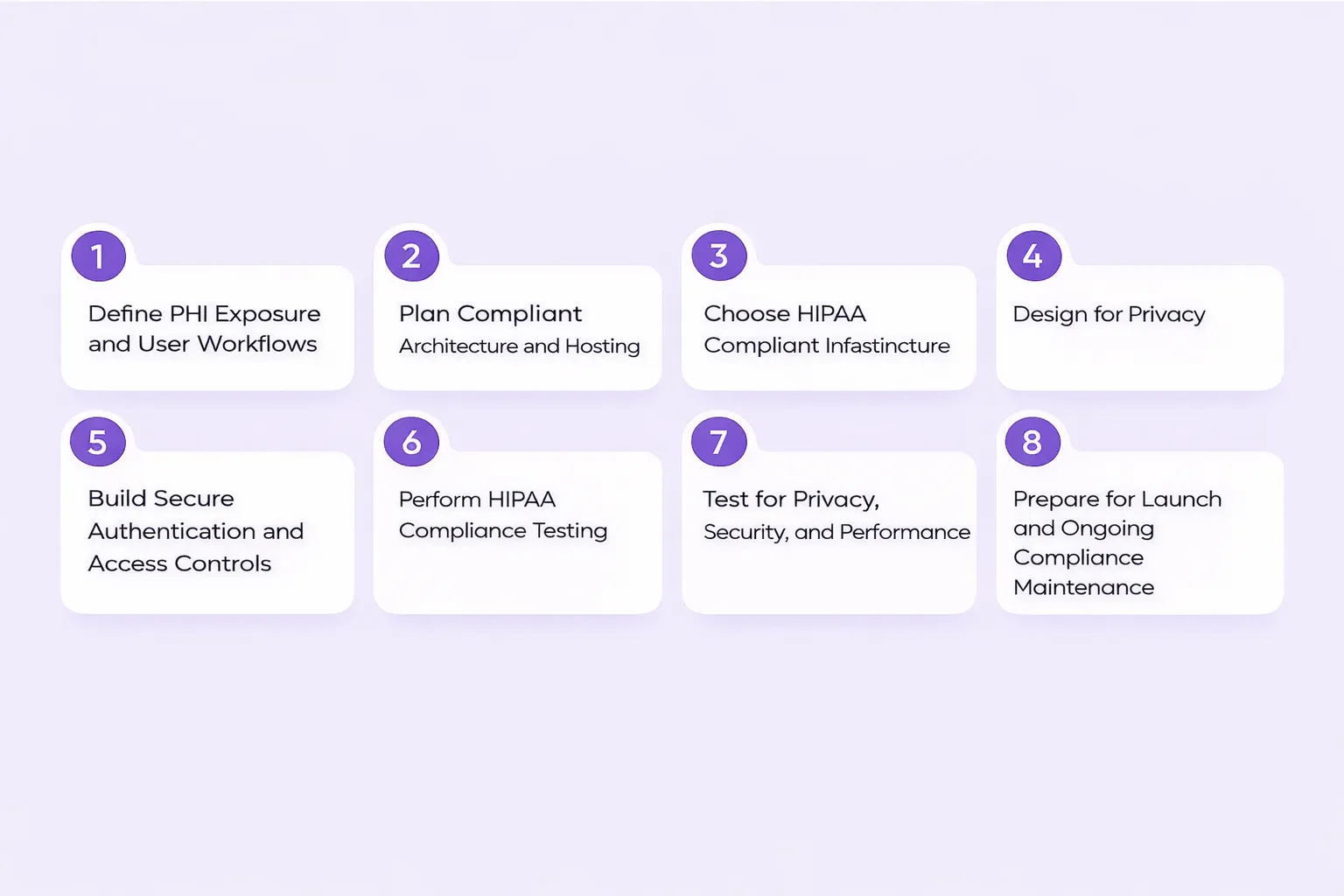
Step-by-Step Process to Build a HIPAA Compliant Healthcare App
A HIPAA compliant healthcare app is not built by adding security features at the end. The process starts much earlier with data mapping, architecture planning, access design, and vendor review. That is what separates a secure healthcare product from one that creates avoidable compliance gaps later.
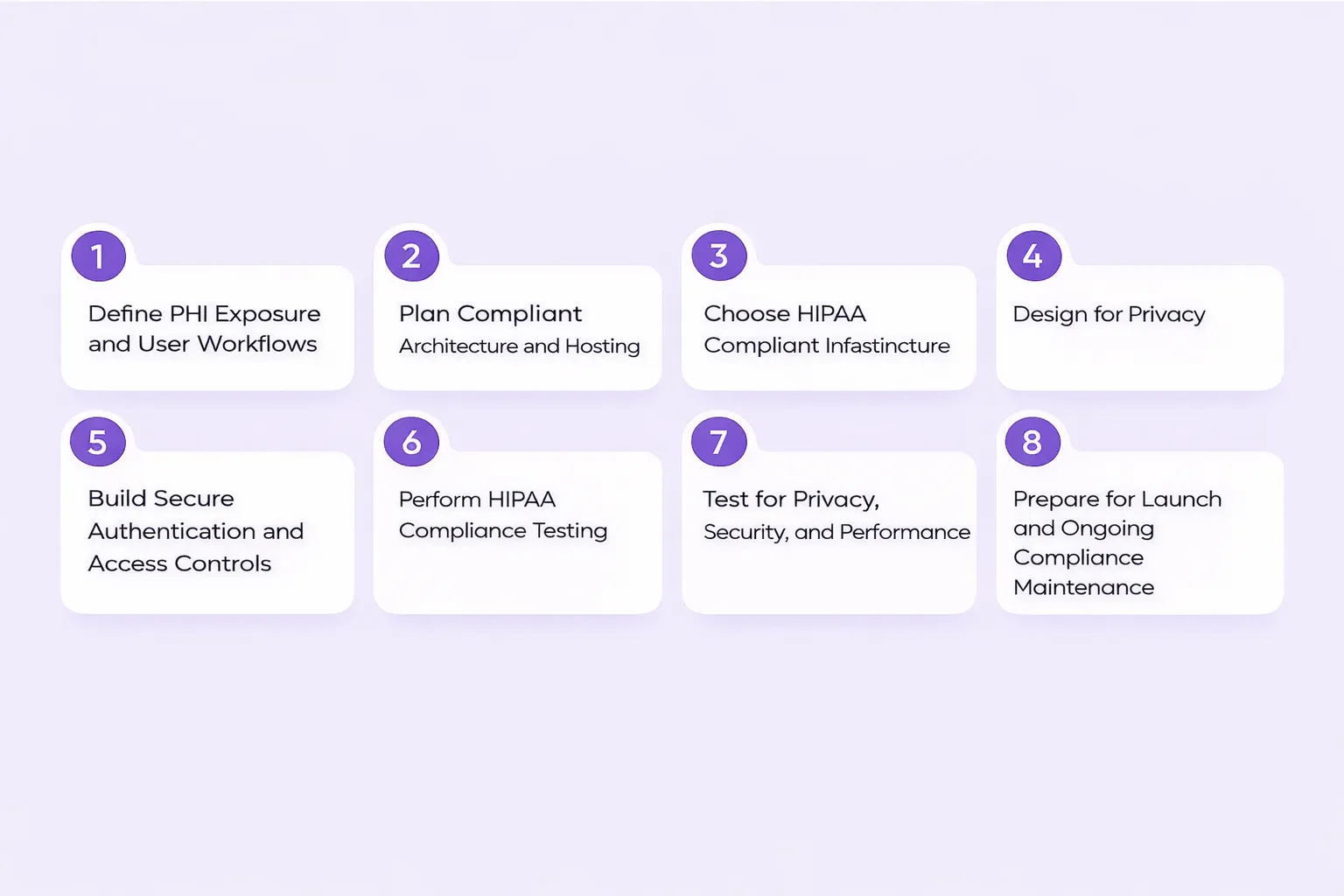
Here’s the step-by-step approach you need to follow to build a HIPAA compliant healthcare app:
Step 1: Define PHI Exposure and User Workflows
The first step in how to build a HIPAA compliant app is identifying where protected health information appears in the product. Teams need to understand what data is being collected, who interacts with it, and how it moves across the system. Without that visibility, compliance decisions become guesswork.
Focus on:
-
What types of PHI does the app collect, store, or share?
-
Which users access that data, including patients, providers, admins, and support teams?
-
Where data enters, moves through, and exits the system?
-
Which workflows involve viewing, editing, exporting, or transmitting sensitive information?
This step creates the foundation for building HIPAA compliant apps in a structured way.
Step 2: Plan Compliant Architecture and Hosting
Once PHI exposure is mapped, the next step is planning the technical foundation. HIPAA compliant app development depends on more than selecting a cloud platform, i.e., a clear architecture that supports secure storage, controlled access, encryption, and recovery from the start.
This stage should cover:
-
Infrastructure and hosting environment selection.
-
Data flow design across frontend, backend, APIs, and storage.
-
Separation of services that handle sensitive health data.
-
Early review of vendors and tools that may touch PHI.
A strong architecture reduces the risk of expensive redesign later.
Step 3: Review Vendors and Sign BAAs Where Needed
Third-party tools often create hidden compliance risk. A healthcare app may rely on cloud providers, communication services, storage vendors, analytics platforms, and external integrations. If these are added without review, they can expose sensitive data in ways the product team did not plan for.
Review:
-
Cloud providers and hosting partners.
-
Messaging and notification platforms.
-
File storage and document handling tools.
-
Third-party systems that process or store PHI.
Where applicable, sign a Business Associate Agreement with vendors handling PHI. This is a core part of developing a HIPAA compliant app, not an administrative detail to leave for later.
Step 4: Build Secure Authentication and Access Controls
Access control is one of the most important parts of how to make your app HIPAA compliant. The system should define exactly who can access what, under which conditions, and for how long. Generic user access models are not enough for healthcare products.
Build this layer around:
-
Role mapping for patients, clinicians, staff, and administrators.
-
Strong authentication controls, including MFA where appropriate.
-
Automatic session timeout and secure session behavior.
-
Least-privilege access rules for sensitive workflows and records.
If access logic is weak, the rest of the security model starts breaking down.
Step 5: Develop Secure Backend and Integrations
The backend is where many healthcare apps either become reliable or become risky. APIs, databases, file storage, and integrations with EHR or EMR systems must be designed to protect data in transit and at rest. Every connection adds complexity and increases the compliance surface area.
Key priorities include:
-
Secure API design and controlled data exchange.
-
Encrypted storage and backend data protection.
-
Safe EHR or EMR connectivity.
-
Limiting unnecessary data exposure across integrations.
This is why developing a HIPAA compliant app requires deeper backend discipline, not just secure screens and user flows. Like any hospital or healthcare provider, you must follow HIPAA’s privacy and security rules. especially when integrating AI in healthcare apps.
Step 6: Implement Auditability and Monitoring
A secure healthcare app should not only protect data, but also show what happened, when it happened, and who was involved. Auditability is critical for operational visibility, risk management, and compliance readiness.
This usually includes:
-
Logs for logins, access events, and record updates.
-
Monitoring for unusual behavior or failed access attempts.
-
Alerts tied to suspicious activity or system issues.
-
Traceability across user actions and sensitive workflows.
HIPAA compliant mobile app development depends on this visibility because untracked systems are hard to trust and harder to defend.
Step 7: Test for Privacy, Security, and Performance
Testing should go beyond basic functionality, because a healthcare app needs validation across privacy controls, security behavior, backend flows, integrations, and misuse scenarios. Standard QA alone is not enough when sensitive health data is involved.
Testing should include:
-
Functional QA for core workflows.
-
Penetration testing and security validation.
-
API testing for secure data exchange.
-
Access misuse scenarios and permission boundary checks.
If a team is serious about how to build a HIPAA compliant mobile app, testing must reflect real compliance and security risk, not just product usability.
Step 8: Prepare for Launch and Ongoing Compliance Maintenance
Compliance does not end when the app is released. Launch preparation should include not just deployment readiness, but also operational controls that support long-term security and reliability. This is where many teams underestimate the real work involved in building HIPAA compliant apps.
Before and after launch, plan for:
-
Secure backups and recovery readiness.
-
Internal documentation and system visibility.
-
Ongoing monitoring and incident response processes.
-
Regular updates as workflows, threats, and integrations change.
HIPAA compliant app development is an ongoing discipline. Teams that treat it as a one-time launch milestone usually create more risk later.
Suggested Read: The Complete Guide to Healthcare App Development
Core Features of a HIPAA Compliant Healthcare App
A HIPAA compliant healthcare app needs features that support secure access, controlled data handling, operational visibility, and continuity planning across the product. For teams exploring how to build a HIPAA compliant app, these are the core capabilities that should be built into the system from the start.

1. Secure User Authentication And Session Management
Authentication is the first layer of protection in HIPAA compliant app development. Healthcare apps should support unique user identification, strong password policies, multi-factor authentication, and secure login controls that reduce unauthorized access.
In some cases, biometric verification may also be appropriate. Session management matters just as much. Automatic logoff after inactivity, secure session handling, and protections against repeated failed login attempts help reduce risk across patient, provider, and admin workflows.
2. Role-Based Access Control
Not every user should see the same data. A healthcare app should define access levels clearly for patients, providers, administrators, and internal staff. Role-based access control limits exposure by giving each user only the permissions required for their responsibilities.
This minimum necessary access model is a core part of building HIPAA compliant apps that can scale securely without exposing more PHI than needed.
3. Encrypted Storage And Secure Communication
Protected health information should be secured both at rest and in transit. That means encrypting stored data in databases, files, and backups while also protecting information moving through APIs, messaging systems, and connected services.
Secure file handling is equally important, especially for apps that manage reports, prescriptions, patient records, or uploaded documents. For teams focused on developing a HIPAA compliant app, encryption cannot be limited to one layer of the system.
🔐 Developer Tip: Even for a HIPAA-compliant mobile app, local storage should be encrypted, especially if the app supports offline use.
4. Audit Trails And Access Visibility
A HIPAA compliant healthcare app should be able to show who accessed sensitive data, what actions were taken, and when they occurred. Audit trails help log user activity, track changes to protected health information, and monitor access events across the system.
This visibility supports compliance reviews, security monitoring, and incident investigation. Without proper auditability, it becomes much harder to prove control over PHI.
5. Secure Backup, Recovery, And Data Destruction
Healthcare apps also need strong data lifecycle controls. Secure backups should be created regularly and protected with encryption so critical information remains recoverable during outages or failures.
At the same time, apps should have secure data destruction mechanisms for deleting PHI from systems, devices, or storage locations when required. That prevents sensitive information from being recovered after deletion and supports better long-term data governance.
6. Secure Messaging, Notifications, And Emergency Access
If the app includes patient-provider communication, it should support secure messaging rather than standard consumer chat patterns. Alerts, reminders, and notifications also need controls to prevent unnecessary exposure of sensitive details.
In addition, healthcare products should plan for emergency mode operation, where critical information remains available under controlled conditions during outages, disruptions, or urgent clinical situations. That makes the app more dependable in real-world healthcare environments.
7. Admin Controls And Operational Oversight
Administrative visibility is essential for managing users, permissions, and system behavior over time. A strong healthcare app should include permission management, reporting, and oversight tools that help teams monitor account activity and enforce access rules.
These controls turn HIPAA compliance from a checklist into a manageable operating model.
What a HIPAA Compliant App Architecture Should Include
A HIPAA compliant healthcare app is not defined only by its features or interface. The architecture behind the product is what determines how protected health information is stored, transmitted, accessed, and monitored across the system. For teams evaluating how to build a HIPAA compliant app, strong architecture is what turns compliance requirements into a working and scalable product foundation.
Frontend, Backend, And Secure API Layer
The frontend should support secure session management, automatic logoff, and controlled access across mobile and web interfaces. Behind that, the backend must manage role-aware APIs, request validation, and secure business logic for handling PHI.
The API layer should control how data moves between frontend apps, backend services, and external systems. In HIPAA compliant app development, controlled data exchange matters just as much as the user experience.
Identity, Access, And Data Storage Layers
A secure architecture should include identity and access management from the start. That means strong authentication, multi-factor authentication where needed, role-based access control, and in some cases attribute-based access control for more complex environments.
On the data side, PHI should be protected through encrypted databases, secure file storage, and strict storage controls. For healthcare teams building HIPAA compliant apps, access should always follow the minimum necessary principle, and stored data should be minimized or de-identified wherever possible.
Logging, Monitoring, And Incident Visibility
The system should include tamper-resistant audit logs that record who accessed, changed, or deleted PHI and when those actions occurred.
Monitoring systems and security alerts should help teams detect unusual behavior, failed access attempts, and system-level issues quickly. This operational visibility is critical for investigations, compliance reviews, and long-term risk management.
Third-Party Integrations And Vendor Risk
Healthcare apps often depend on external services such as EHR or EMR systems, payment platforms, messaging tools, analytics systems, and cloud providers. Every integration increases the compliance surface area.
That is why vendor review is essential. If a vendor handles PHI, a Business Associate Agreement may be required. Choosing cloud infrastructure from providers such as AWS, Azure, or Google Cloud that can support HIPAA requirements and sign a BAA is a foundational architecture decision.
Estimated Cost and Timeline for HIPAA Compliant Healthcare App Development
HIPAA compliant healthcare app development typically ranges from $50,000 to $400,000+, depending on complexity, integrations, and compliance requirements. Security layers, EHR connectivity, and testing depth are the primary cost and timeline drivers.
| App Type |
Estimated Cost (USD) |
Timeline |
Typical Scope |
| MVP / Basic App |
$40,000 – $100,000 |
3 to 5 months |
Limited features, basic workflows, minimal integrations, core compliance controls |
| Mid-Level App |
$100,000 – $250,000+ |
6 to 9 months |
Multiple user roles, EHR/EMR integrations, admin panel, enhanced security layers |
| Enterprise / Complex App |
$250,000 – $500,000+ |
10 to 18 months |
Advanced workflows, multiple integrations, high scalability, deep compliance and monitoring systems |
Suggested Read: Custom mobile app development cost
Why Healthcare Teams Choose Quokka Labs for Secure App Development
Healthcare app development requires more than fast delivery. It demands strong product thinking, secure architecture, careful integration planning, and a clear understanding of how sensitive healthcare workflows operate in practice. As an experienced app development company, Quokka Labs helps healthcare teams build digital products with that broader perspective from the start.
Our strengths include:
-
Compliance-aware product planning that helps teams make better decisions around data flows, access control, and system design.
-
Secure mobile and web app development for patient, provider, admin, and operational workflows.
-
Strong UI/UX thinking that keeps healthcare products usable without compromising security and control.
-
Scalable engineering support across architecture, development, integrations, testing, and post-launch growth.
This gives healthcare teams a more reliable path to building secure, scalable products with fewer avoidable gaps in delivery, usability, and compliance readiness.
Conclusion
HIPAA compliant healthcare app development is not just about meeting a regulatory requirement. It is about building a product with secure architecture, controlled data handling, operational readiness, and long-term risk management built in from the start. The strongest healthcare apps are planned around compliance early, not patched later through isolated fixes.
For teams evaluating their next healthcare product, the right development approach reduces risk before it turns into rework, delays, or security exposure. Quokka Labs helps businesses build healthcare applications with stronger technical foundations, clearer execution, and a more reliable path to secure growth.
Frequently Asked Questions
How to make an app HIPAA compliant?
A healthcare app becomes HIPAA compliant when it protects PHI through the right mix of technical, administrative, and operational controls. That usually includes secure authentication, role-based access, encryption, audit logging, secure infrastructure, backup and recovery planning, vendor review, and ongoing monitoring. HIPAA compliant app development depends on how the full system handles sensitive data, not just on one security feature.
Dos encryption alone make an app HIPAA compliant?
No. Encryption is essential, but it is only one part of HIPAA compliant healthcare app development. A compliant app also needs proper access control, audit trails, secure authentication, session management, vendor oversight, and monitoring. If teams focus only on encrypting data and ignore the rest of the system, the app can still create compliance and security risk.
Do third-party vendors need to sign a BAA?
If a third-party vendor handles, stores, processes, or transmits PHI, a Business Associate Agreement may be required. This often applies to cloud providers, storage platforms, communication tools, and certain integrations. When developing a HIPAA compliant app, vendor review should happen early because third-party services can create major compliance gaps if they are added without checking PHI exposure and BAA requirements.
What features should a HIPAA compliant healthcare app include?
A HIPAA compliant healthcare app should include secure user authentication, multi-factor authentication where needed, role-based access control, encryption at rest and in transit, audit logs, automatic session timeout, secure messaging, backup and recovery support, and strong admin controls. The exact feature set may vary by product, but these controls are central to building HIPAA compliant apps that can operate securely at scale.
How long does HIPAA compliant healthcare app development take?
The timeline depends on the scope, workflows, integrations, and compliance requirements of the product. A simpler MVP may take around 3 to 5 months, while mid-level healthcare apps often take 6 to 9 months. More complex or enterprise-grade platforms can take 10 to 18 months or longer. Discovery, architecture planning, EHR or EMR integration, and compliance-focused testing usually extend delivery timelines.


 Facebook
Facebook
 Twitter
Twitter
 LinkedIn
LinkedIn
 Pinterest
Pinterest